MHA issues Advisory on Secure use of ZOOM Meeting Platform
The Cyber Coordination Centre (CyCord), under the Union Ministry of Home Affairs (MHA), has issued an advisory on secure use of ZOOM Meeting Platform by private individuals. This advisory states that the platform is not for use by Government officers/officials for official purposes.
The document makes reference to earlier advisories of the Indian Computer Emergency Response Team(Cert-In) and states that Zoom is not a safe platform. The guidelines have been issued to safeguard private individuals who would still like to use the platform for private purposes.
The broad objective of this advisory is to prevent any unauthorized entry into a Zoom Conference Room and prevent the unauthorized participant to carry out malicious attacks on the terminals of other users in the conference.
The details of protective measures to be taken by individuals are as follows:-
Advisory on Secure use of Zoom meeting platform by private individuals (not for use by government offices/officials for official purpose)
Zoom is a not a safe platform and advisory of cert-in on the same dated Feb 06, 2020 and March 30, 2020 may kindly be referred. These advisories are available on Cert-In website.
2. Those private individuals who still would like to use Zoom for private purpose may kindly follow the following guidelines.
3. Broad objective of this document is to enable/disable certain settings is to:
- prevent unauthorised entry in the conference room
- prevent an authorised participant to carry out malicious on the terminals of other in the conference.
- Avoid DOS attack by restricting users through passwords and access grant.
4. Most of the settings can be done by login into users zoom account at website, or installed application at PC/Laptop/Phone and also during conduct of conference. However certain settings are possible through certain mode/channel only. For example, lock meeting can be enabled by administrator only when the meeting has started. This documents explains in details all the security configuration through website, App and through console during the conduct of conference
Objective of security configurations:
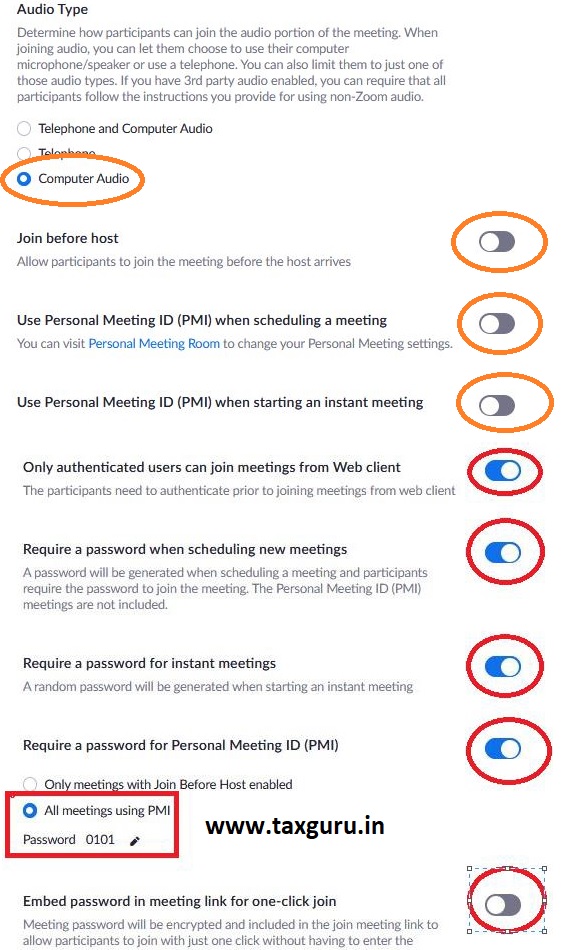
1. Setting new user ID and password for each meeting
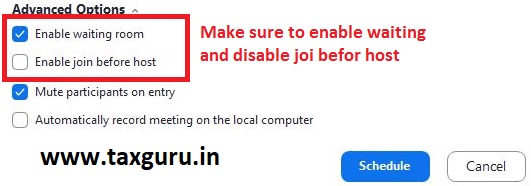
2. Enabling waiting Room, so that every user can enter only when host conducting meeting admits him
3. Disabling join before host
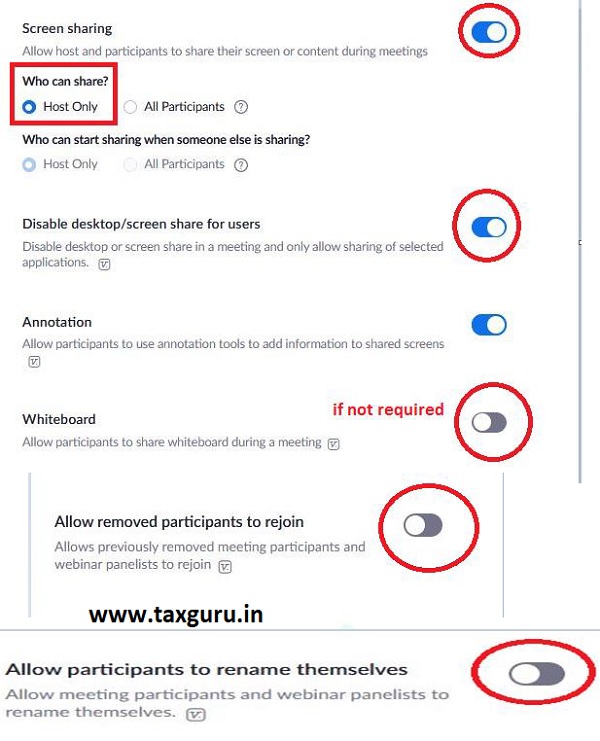
4. Allowing Screen Sharing by host Only
5. Disabling “Allow removed participants to re-join”
6. Restricting/disabling file transfer option (if not required)
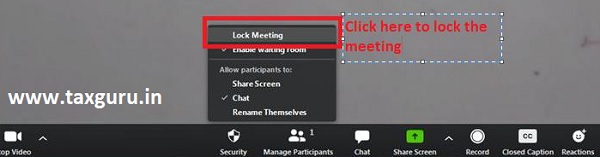
7. Locking meeting, once all attendees have joined
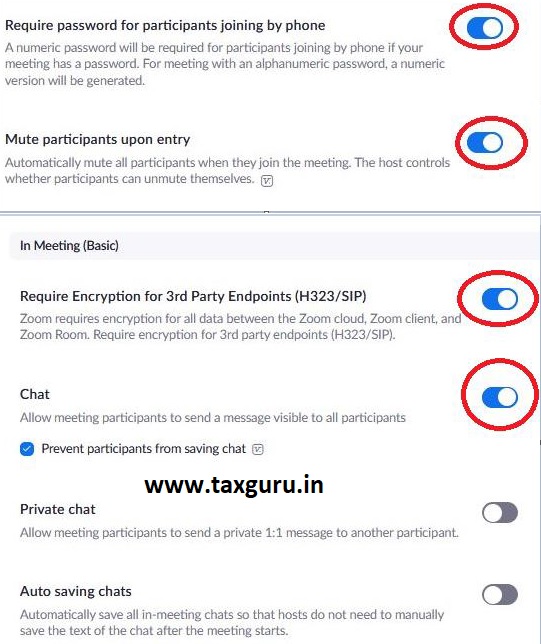
8. Restricting the recording feature
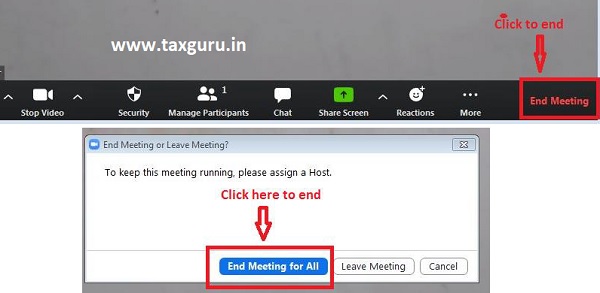
9. To end meeting (and not just leave, if you are administrator)
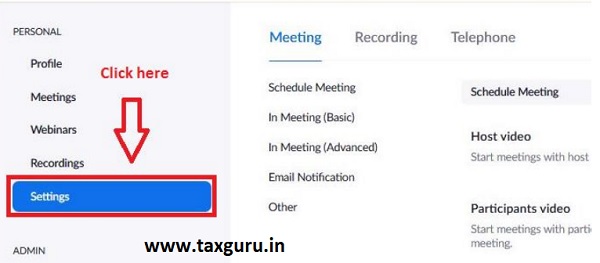
Section 1: Security Configuration Through website
1. Logging into zoom Website: https://zoom.us/ by entering your account credentials

2. After login, page looks like this. Three important and useful links are shown in red boxes, profile, setting and personal meeting ID

3. Click profile-> edit button in front of personal meeting ID shown in above diagram and un-check the box shown below and click save changes.

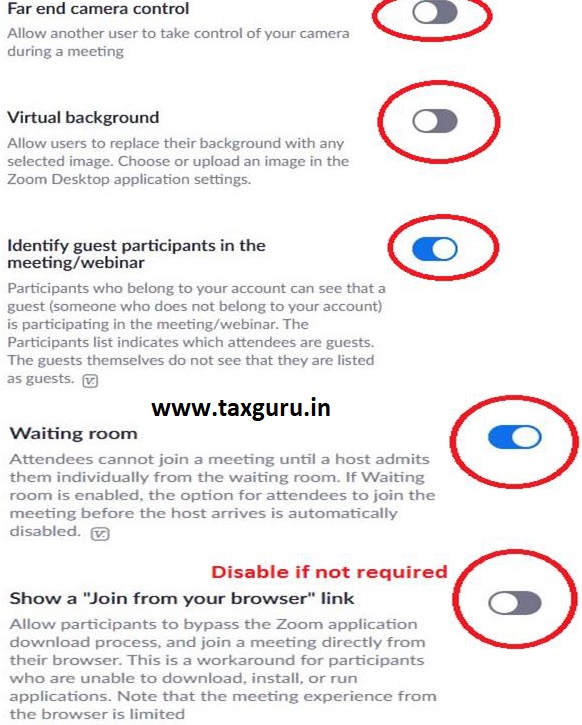
4. Click the setting on home page and keep on scrolling down the window and make necessary configuration as shown in figures below. Only important ones are marked in red boxes and others could be anything
–
–
–
–
Section 2: Security Configuration Through App
1. Zoom meeting App when launched look like this:
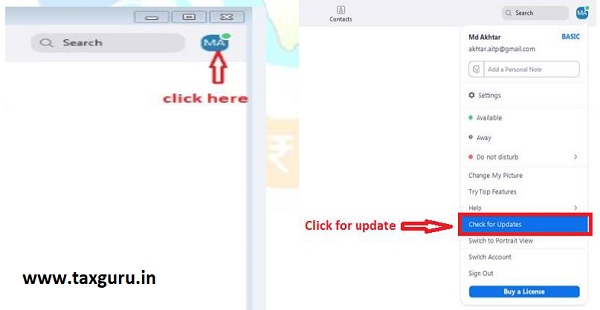
2. Update your App: First and fore most important thing is to update your Zoom App:
- click menu -> navigate to check for update -> click
3. Set a password for personal meeting ID and enable waiting
- click edit in meeting as shown below

- Check password box, enter a strong password, check enable waiting window etc. desirable settings are shown in red boxes and click save

4. Avoid conducting meeting by using Personal Meeting ID (PMI).
Clicking on start as shown below will start a meeting with personal meeting ID and password set by user as shown above. In this case PMI: 3452161630 and password: Sc@3Q*
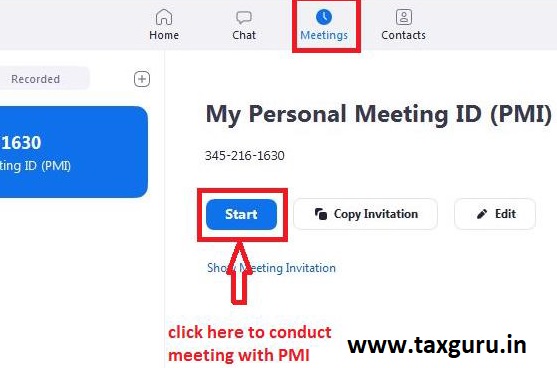
Problem in suing personal meeting ID is that with PMI and password is fixed. It does not automatically change with every new meeting.
5. Conduct a new meeting with randomly generated ID and password instead of fixed one as shown above
- Click on home
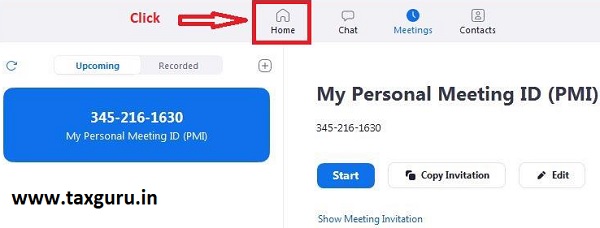
- Click New Meeting drop down as shown below

- Un-check use My Personal Meeting ID (PMI), if not already done
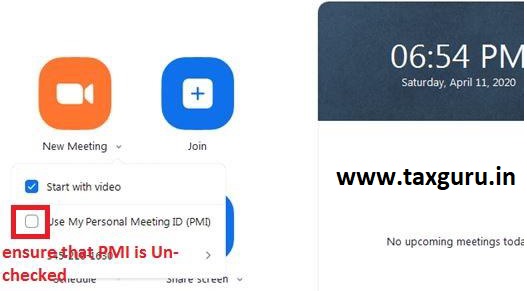
- Click new meeting icon to start a new meeting
![]()
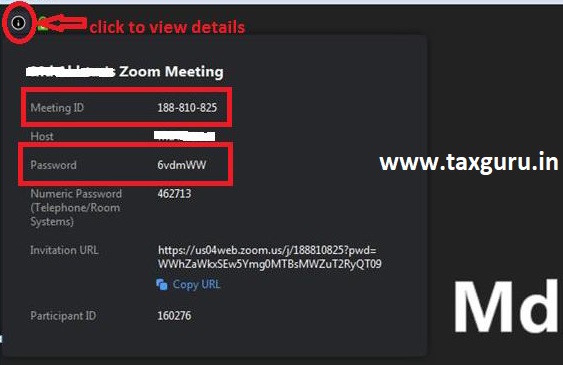
- Once Meeting has started, you will see your meeting ID and password by clicking left top icon below. it will be random and change with every new meeting.
6. Scheduling a meeting with randomly generated ID and password
- Click schedule as shown below
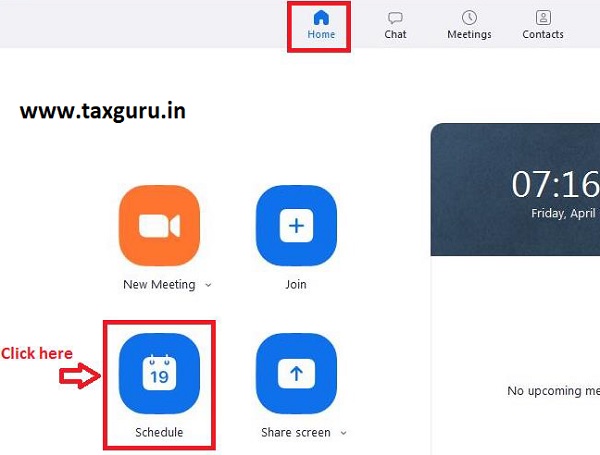
- The window as shown below will open up
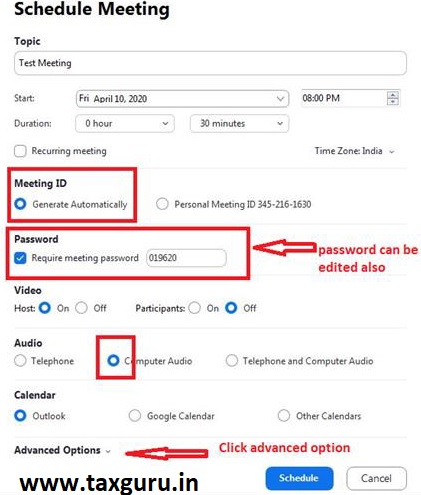
- After clicking advanced Options shown in above window following expansion will open and do setting as shown below.
6. Lock the meeting session, once all attendees have joined
- Once meeting is in progress, control bar looks like this

- Click Security and click on Lock Meeting, if all your participants have joined. you can enable waiting room from here also. you can also disable share screen by users from here
Miscellaneous tips:
- Don’t use your personal meeting Id (PMI) to host event, instead use randomly generated meeting IDs for each event.
- Don’t share your link on public platform, instead share randomly generated meeting id and password for every new meeting session/schedule. It makes it much secure and difficult to leak.
- If you are admin, remember to end meeting, dont just leave meeting.
- Sign out of your account when not in use
Disclaimer: Information provided here is based on open source without warranty of any kind.




